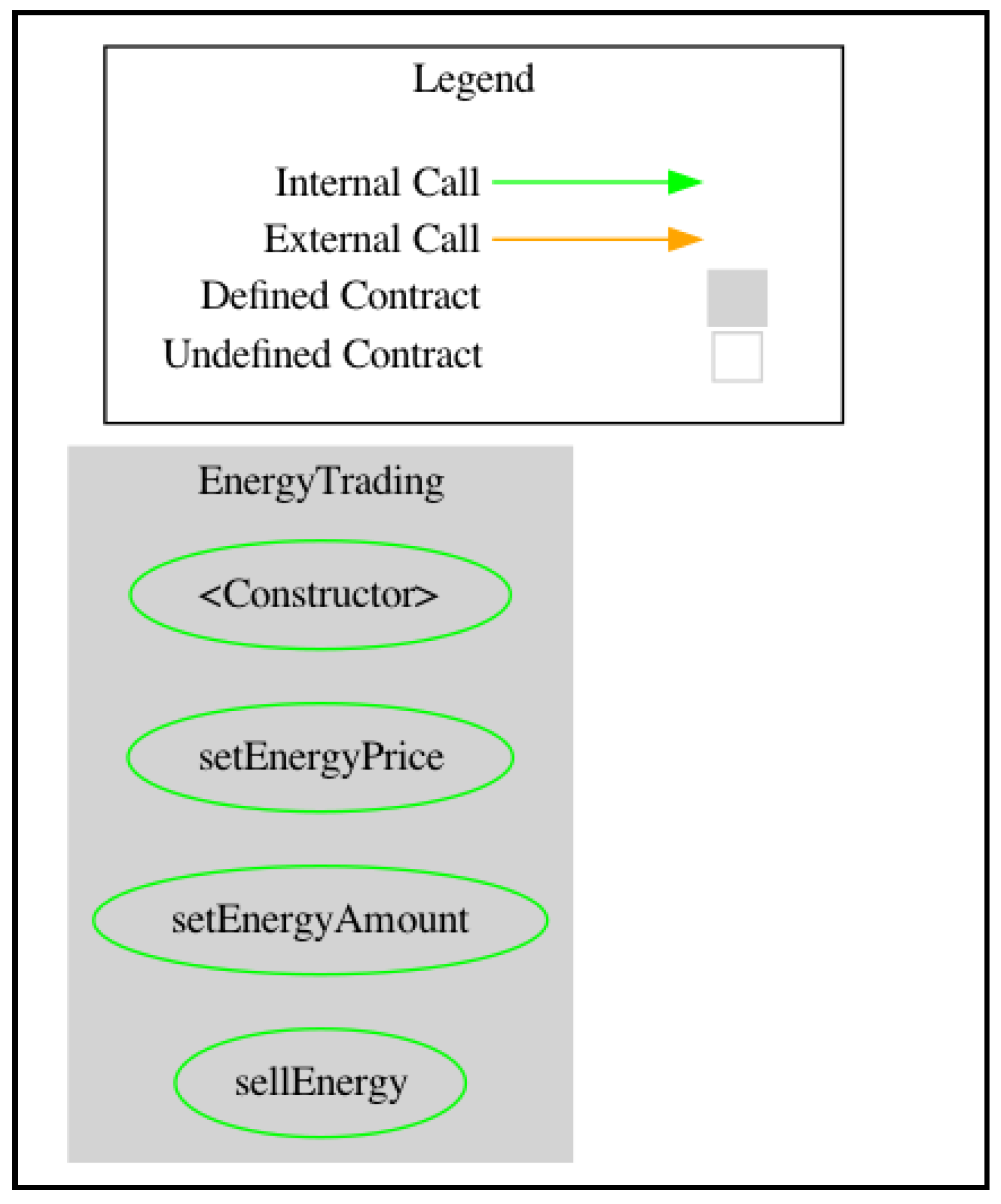
Information | Free Full-Text | Evaluation of Smart Contract Vulnerability Analysis Tools: A Domain-Specific Perspective

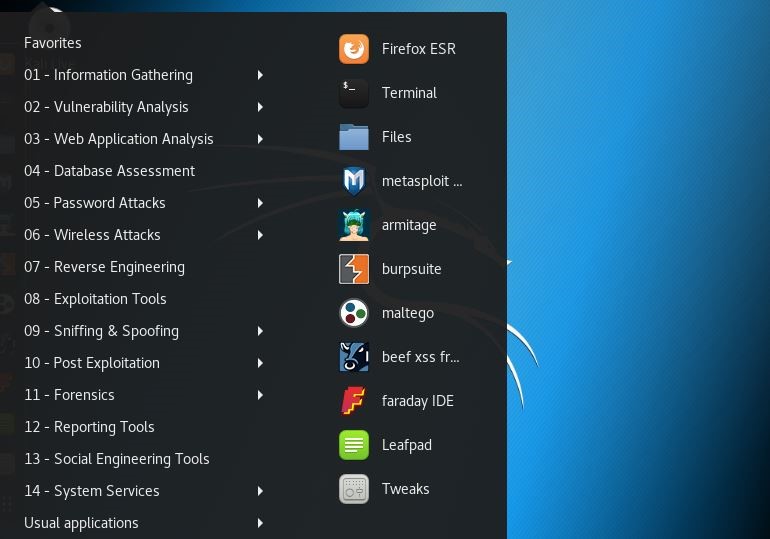
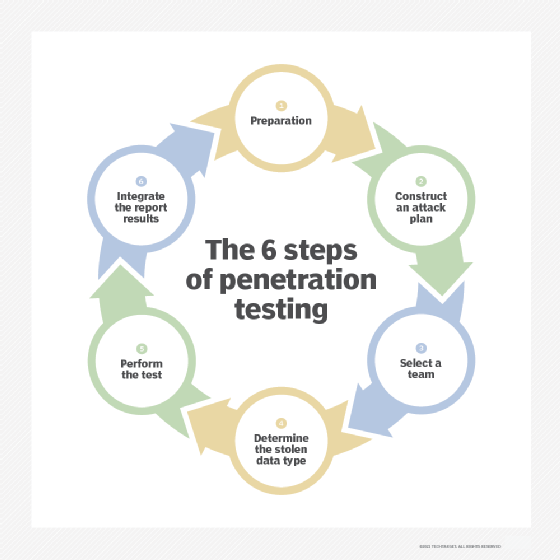
Penetration testing: choosing the right (Linux) tool stack to fix your broken IT security | by David Clinton | HackerNoon.com | Medium